انتقل إلى وضع عدم الاتصال باستخدام تطبيق Player FM !
Problems Plague Second Auth
Manage episode 307446607 series 2994871
Websites are requiring that you provide a text message for a false sense of security. Two methods of defeating 2nd auth are explained in this episode and a strategy for security that you should adopt.
Problems Plague Second Auth
Every day Big Tech and Mass Media make it hard to find out what is going on with the internet. The suppression of information is a danger to all of us. Social media attempts to shape news and information by over-amplification of disinformation. This podcast hope to give information and provide insights from
Join our community!!
Subscribe to the Insecurity Brief podcast now on every platform we can find
Follow me on Twitter
Links
Our Website:
https://www.tripelix.com/insecurity/problems-plague-second-auth/
Youtube:
Rumble:
https://rumble.com/vpc44m-problems-plague-second-auth.html
iTunes:
https://podcasts.apple.com/us/podcast/problems-plague-second-auth/id1583788677?i=1000542311339
Spotify:
https://open.spotify.com/episode/7BPLVDdbMK2KgHQ9GqsxJ8
#2fa #phishing #2ndauth

A New Phone Scam Bypasses Two-Factor Security Codes
ThioJoe
Know about it so you won’t get tricked!

Join the fight against phishing
Timely. Accurate. Relevant Phishing Intelligence.
https://openphish.com/
Catching Transparent Phish: Analyzing and Detecting MITM Phishing Toolkits
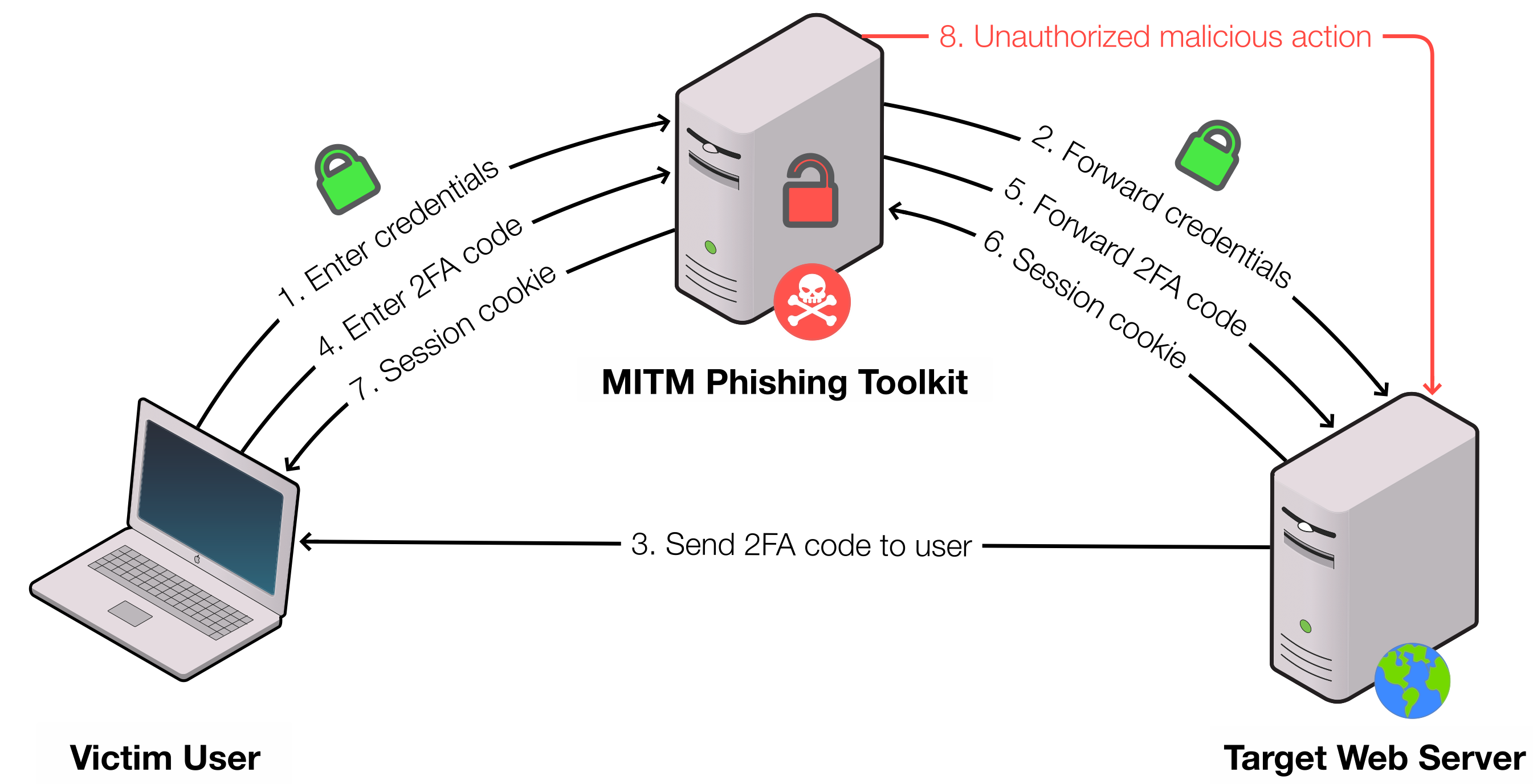
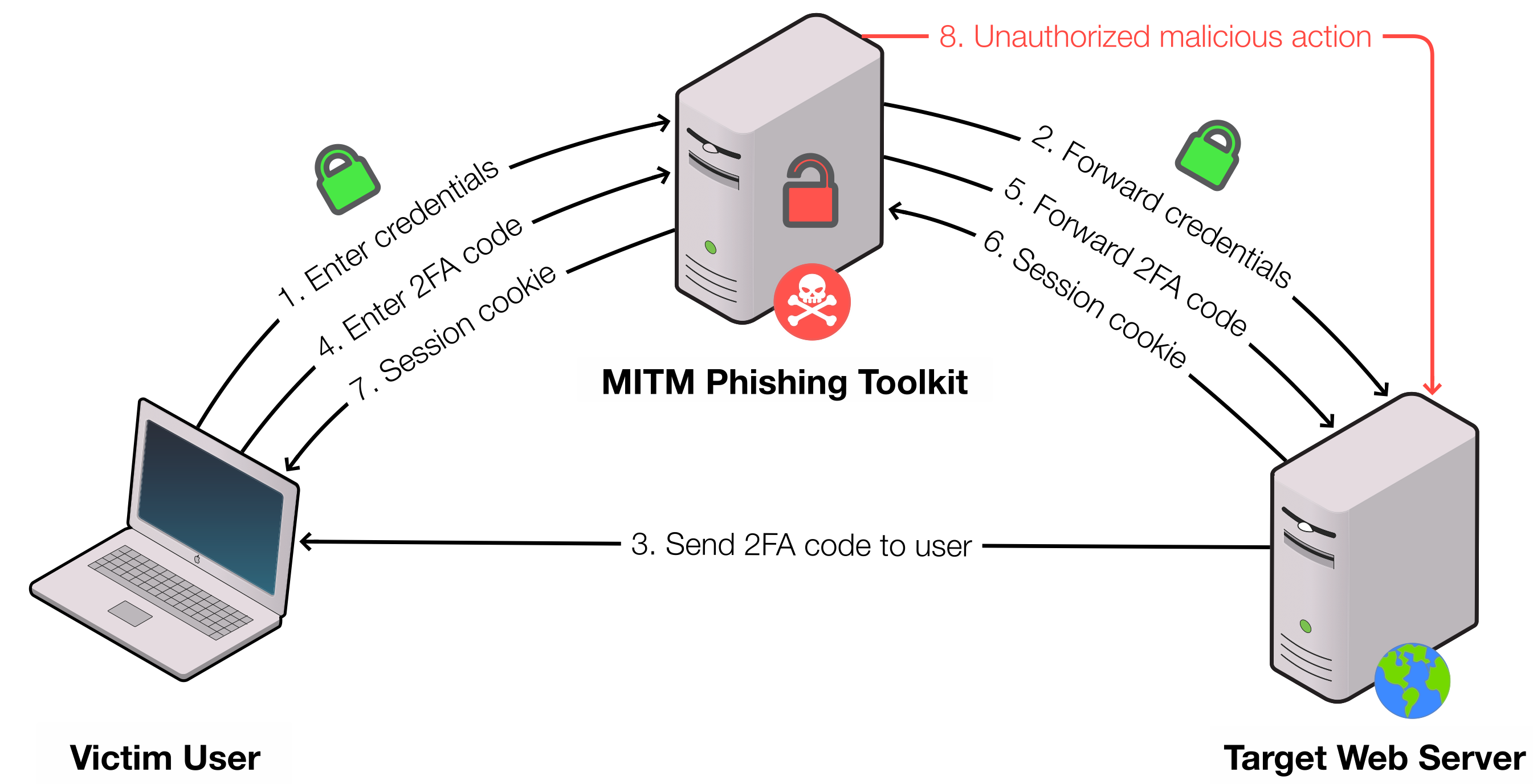
For over a decade, phishing toolkits have been helping attackers automate and streamline their phishing campaigns. Man-in-the- Middle (MITM) phishing toolkits are the latest evolution in this space, where toolkits act as malicious reverse proxy servers of online services, mirroring live content to users while extracting credentials and session cookies in transit. These tools further reduce the work required by attackers, automate the harvesting of 2FA-authenticated sessions, and substantially increase the believability of phishing web pages.
75 حلقات
Manage episode 307446607 series 2994871
Websites are requiring that you provide a text message for a false sense of security. Two methods of defeating 2nd auth are explained in this episode and a strategy for security that you should adopt.
Problems Plague Second Auth
Every day Big Tech and Mass Media make it hard to find out what is going on with the internet. The suppression of information is a danger to all of us. Social media attempts to shape news and information by over-amplification of disinformation. This podcast hope to give information and provide insights from
Join our community!!
Subscribe to the Insecurity Brief podcast now on every platform we can find
Follow me on Twitter
Links
Our Website:
https://www.tripelix.com/insecurity/problems-plague-second-auth/
Youtube:
Rumble:
https://rumble.com/vpc44m-problems-plague-second-auth.html
iTunes:
https://podcasts.apple.com/us/podcast/problems-plague-second-auth/id1583788677?i=1000542311339
Spotify:
https://open.spotify.com/episode/7BPLVDdbMK2KgHQ9GqsxJ8
#2fa #phishing #2ndauth

A New Phone Scam Bypasses Two-Factor Security Codes
ThioJoe
Know about it so you won’t get tricked!

Join the fight against phishing
Timely. Accurate. Relevant Phishing Intelligence.
https://openphish.com/
Catching Transparent Phish: Analyzing and Detecting MITM Phishing Toolkits
For over a decade, phishing toolkits have been helping attackers automate and streamline their phishing campaigns. Man-in-the- Middle (MITM) phishing toolkits are the latest evolution in this space, where toolkits act as malicious reverse proxy servers of online services, mirroring live content to users while extracting credentials and session cookies in transit. These tools further reduce the work required by attackers, automate the harvesting of 2FA-authenticated sessions, and substantially increase the believability of phishing web pages.
75 حلقات
كل الحلقات
×مرحبًا بك في مشغل أف ام!
يقوم برنامج مشغل أف أم بمسح الويب للحصول على بودكاست عالية الجودة لتستمتع بها الآن. إنه أفضل تطبيق بودكاست ويعمل على أجهزة اندرويد والأيفون والويب. قم بالتسجيل لمزامنة الاشتراكات عبر الأجهزة.




